A Group of researchers demonstrated a start-to-finish means of monitoring an encrypted GSM cellphone calls and text messages, using only sub-$15 telephones as network “sniffers,” attached to a laptop computer powered by open source softwares.
A Group of researchers demonstrated a start-to-finish means of monitoring an encrypted GSM cellphone calls and text messages, using only sub-$15 telephones as network “sniffers,” attached to a laptop computer powered by open source softwares.
GSM Security is inherently weak and that’s why it was made possible to Hack GSM Security (GSM’s 64-bit A5/1 encryption), last year. However, governments own devices that are worth $50,000, which essentially monitor phone activities for National security.
“GSM is insecure, the more so as more is known about GSM,” said Security Research Labs researcher Karsten Nohl. “It’s pretty much like computers on the net in the 1990s, when people didn’t understand security well.”
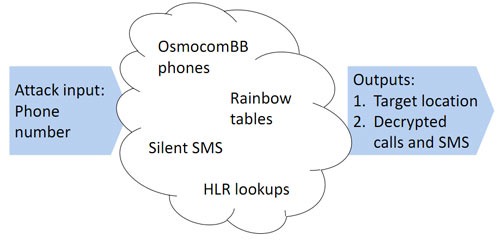
Every aspect of the GSM Hack was demonstrated from start to end including scenarios in which GSM networks exchange subscriber location data, in order to correctly route phone calls and SMSs, allows anyone to determine a subscriber’s current location with a simple Internet query, to the level of city or general rural area. Once a phone’s City is known, a potential attacker can drive through the area, sending the target phone “silent” or “broken” SMS messages that do not show up on the phone. By sniffing to each bay station’s traffic, listening for the delivery of the message and the response of the target phone at the correct time, the location of the target phone can be more precisely identified.
GSM Network Sniffer
Researchers replaced the firmware of a simple Motorola GSM phone with their own, which allowed them to retain the raw data received from the cell network, and examine more of the cellphone network space than a single phone ordinarily monitors. Modifying the USB interface, helped them send this data in real time to a computer, which captured every bit of the information.
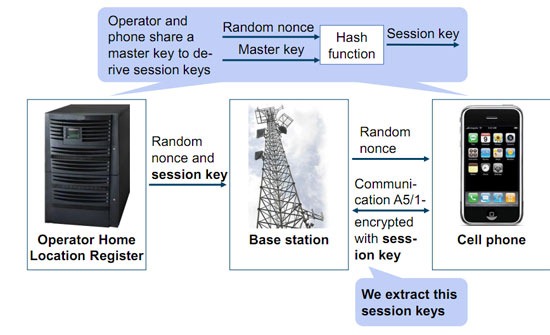
By sniffing the network while sending a target phone an SMS, they were able to determine precisely which random network ID number belonged to the target. This gave them the ability to identify which of the myriad streams of information they wanted to record from the network. After that, the next step is essentially decrypting the information. ITs not that easy, but was made possible by the way operator networks exchange system information with their phones.
As part of this background communication, GSM networks send out identifying information, as well as “keepalive” messages and empty spaces are filled with buffered bytes. Truth be told, a new GSM standard was put in place several years ago to turn these buffers into random bytes, they in fact remain largely identical today, under a much older standard. Sticking to older standards enabled hackers to predict with a high degree of probability the plain-text content of these encrypted system messages. This, combined with a 2 terabyte table of pre-computed encryption keys (a so-called rainbow table), allows a cracking program to discover the secret key to the session’s encryption in about 20 seconds. (Rainbow tables are usually used in all kinds of Brute-force password hacking).
Many GSM operators reuse these session keys for several successive communications, allowing a key extracted from a test SMS to be used again to record the next telephone call, minimizing the need for recomputation.
The process was demonstrated using their software to sniff the headers being used by a phone, extract and crack a session-encryption key, and then use this to decrypt and record a live GSM call between two phones in no more than a few minutes.
Can something be done about GSM’s security?
Any geek can make such devices and with the help of the open source software, can mimic these hacks. So can we really do something to prevent these kinds of hacks from happening?
“Much of this vulnerability could be addressed relatively easily”, Nohl said. “Operators could make sure that their network routing information was not so simply available through the Internet. They could implement the randomization of padding bytes in the system information exchange, making the encryption harder to break. They could certainly avoid recycling encryption keys between successive calls and SMSs”.
“This is all a 20-year-old infrastructure, with lots of private data and not a lot of security,” he said. “We want you to help phones go through the same kind of evolutionary steps that computers did in the 1990s.”
Worst part is, all the current 3G phones are NOT shielded from this hack. Knowing that 3G is primarily used for Data, its now easy to capture any 3G user’s online activity including their passwords and credit card numbers.
Maybe its high time for GSM consortium to wakeup and address these issues, or atleast learn few things from CDMA networks, which are inherently secure.
Resources:
Rainbow tables, Airprobe, Kraken srlabs.de
OsmocomBB firmware osmocom.or
The Video Presentation can be downloaded here: Part1, Part2.
We write about Security, Open Source, Programming, Web, Apple, iPhone,Android and latest in Tech @taranfx on Twitter or by subscribing below:
loading...
loading...