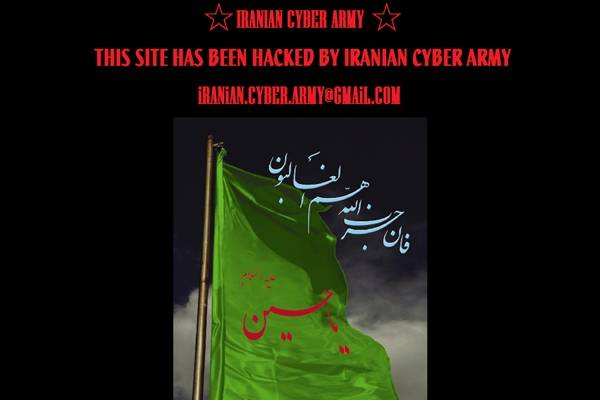
 Internet faced World Wide Panic as Twitter.com was defaced to run out of service. Soon after the attack Users were able to see a page that claimed work of “Iranian Cyber Hackers”.
Internet faced World Wide Panic as Twitter.com was defaced to run out of service. Soon after the attack Users were able to see a page that claimed work of “Iranian Cyber Hackers”.
In simple words, it was nothing but a DNS hijacking attack in which Twitter’s DNS records were altered. That means surfers trying to reach the website directly via name resolution services were redirected to a fake domain, while the Twitter servers were running. As a result, applications that depended upon Twitter’s API – such as TweetDeck or mobile phone apps – were unaffected by the attack. Hence, Twitter servers were never hacked!
Rik Ferguson, a security consultant at Trend Micro, explains that this type of DNS hijacking usually involves compromising the systems at the registrar responsible for the DNS records of the victim company before altering the relevant DNS records, in a blog posting here.
This kind of DNS hijacking usually involves compromising the registrar responsible for the DNS records of the victim company, the attackers then make unauthorised changes to the DNS records. These changes mean that when someone types a address into browser, we are directed Not to the real web site but to a second site, set up by the hackers, in this case the “Iranian Cyber Army”. This has the net effect of making it look like, in this example, servers belonging to Twitter were compromised when in reality that was not the case.
When it comes to attacking high profile targets it can often be that the registrar is the most vulnerable point in the security armour. In fact Zone-H, the defacement archive, has previously noted that registrars have been “one of the main aims of the past months”. Once a Registrar is compromised, it becomes very easy to alter DNS records, updating NameServers alone does the trick.
As Hacking as a Service Prevails, DNS attacks had been common. DNS has had several vulnerabilities in the past, these sorts of attacks are usually limited to hacktivism activities. Companies should be monitoring their DNS resolution on several servers to become aware as early as possible when this kind of attack takes place.
loading...
loading...

It seems as though no one is safe from some kind of hacking attempt.
loading...
loading...