 If you thought cookies reveal alot about your identity over the internet, probably you need to rethink. A new type of tracking is now considered to be way more powerful, and yet you don’t have a clue about it.
If you thought cookies reveal alot about your identity over the internet, probably you need to rethink. A new type of tracking is now considered to be way more powerful, and yet you don’t have a clue about it.
The method grabs a large amount of data about your browser, such as plug-ins, system fonts, and your operating system, screen resolution, etc. Each one when considered alone, they don’t identify you. But when collaborated, they’re a digital fingerprint: A Digital replica of you identity on the web.
It’s like describing a person. Just saying “blonde hair” won’t identify anyone. But add in “5 feet, 11 inches tall,” “mole on left little finger”, “versace glasses,” and so on, and soon you have enough information to pull someone out of a crowd, even without their name, PAN/SSN, or any facial recognition.
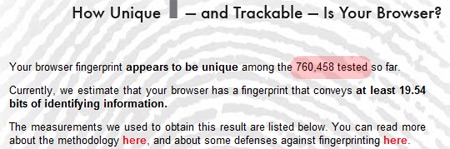
Probably, if you are concerned, you might consider taking a “safe” test at Panopticlick.eff.org. Panopticlick gathers little details about your browser and computer, mostly using Javascript. For what I tested my Chrome with, it claims to to uniquely identify my surfing out of more than 760,458 visitors. And the fact is, more than 90% of them are unique. In other words, there’s 9/10 chance that your identity is unique and you are traceable wherever you go.
Some Background
Electronic Frountier foundation, (founder of the Panopticlick project) claim that it’s accurate to high degree.
But who Invented. Unlike most bad intentions behind privacy lapses, the original intent of Browser Fingerprinting was to prevent Banking Frauds. Often hackers used anonymous proxies to deface websites, but since the browsers stayed the same (in most cases, if not all), they were still back-traceable.
Privacy issues
Things often take a different shape with time. As PCWorld notes, Scout Analytics, a publisher’s analytics tool, collects not just browser data but also some advanced fingerprints like how you type–things like your typing speed and typing patterns.
The data is all collected using javascript alone, and therefore very hard to prevent. The company says that it sells its service primarily to paid subscription sites, such as those offering real estate listings, and that it is keen to expand into marketing and advertising by helping sites track visitors in a way that, as he notes, is more accurate than using cookies. (Cookies can be deleted, which makes a repeat visit look like a new person to the site.)
Short of in-depth analysis of a given page, browser fingerprinting doesn’t leave tracks, so it’s hard to pinpoint sites that use it. But clearly advertisers want accurate tracking.
Does Law stop it?
The question is can sites legally use this fingerprinting? Existing guidelines from the Network Advertising Initiative wouldn’t allow it if a target had opted out of it for use in behavioral advertising.
But these hardly apply anywhere except for few states in US. There is no clear cut law on this for the web.
Counterfeiting Browser Fingerprinting
Virtually, reading every website’s Privacy Policy could help understanding their tracking, but it’s way too distant dream for each user to read each one of those websites.
EFF has listed some critical ones that can help you stay out of the mess, but they are not as easy as deleting a cookie. Most important among them are:
- Try using a non-rare browser i.e. use a browser which is popular. This way you owe higher chances of duplicating someone else’s fingerprint thereby making your signature non-unique.
- Disable Javascript: this is impossible to do if you live on the modern web, but when possible do it. Usage of addons/extensions like NoScript can be considered better but you can endup blocking Ads and ad Blocking is devastating to the sites you love.
- Use TorButton: Tor button addon strips-off some private ids like useragent strings and “Standardizes” them for making it hard to backtrace.
- Use “Private Browsing” Almost all modern browsers like Firefox, Opera, Chrome support Private browsing which protect their users against fingerprint tracking
We write about Google, Twitter, Security, Open Source, Programming, Web, Apple, iPhone,Android and latest in Tech @taranfx on Twitter or by subscribing below:
loading...
loading...

Facebook: The End of Privacy: http://bagtheweb.com/b/lxYGFU
Message to add sites that document the erosion of privacy on Facebook. #privacy
loading...
loading...