Its time for revelation of various hacks from your home security system to cars which rely on wireless key locks, as the BlackHat 2014 conference kicks-off.
At this year’s BlackHat conference, various hacks in security systems have been unveiled. The most shocking being an eavesdropper unlocking your car, without having any prior knowledge about your car or you.
Silvio Cesare, an Australian wireless researcher, has developed a way to spoof a wireless key fob that works well with popular cars. With off-the-shelf wireless radio tools costing $1000, he can hack wireless security system of cars. So what this means is that your keyless car entry is going to have a big toll on you. He has said to have tested the hack against his own 10-year old car, which he claims is among the best selling cars in his country. But he claims that car makers tend to source keyfobs from common manufacturers (like Amtel, TRW), making most make/model vulnerable to this kind of security attack.
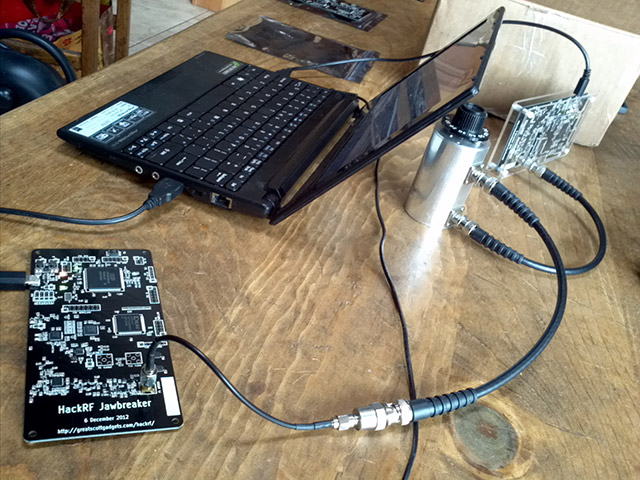
Cesare uses a Software-defined radio, a software controlled radio device that can be programmed to work with wide set of frequency bands from Mhz (FM, GSM) to Ghz (Bluetooth, Wifi, etc). This mini radio setup is capable of operating as FM transmitter, GSM cell tower, or even bluetooth sender, and Wifi AP/client.
Step 1. Acquisition
With the hardware attached to his laptop, he can capture the frequency range in which keyfob operates and analyze the frequency modulation it uses for communication. With his tests he found most of these keyfobs operating in mhz bands using FM (frequency modulation).
Car security lock keyfobs generate different frequencies on each press. This is a time variant function, a set of frequency will only be used once and it will generate an entirely random set of frequencies next time to unlock the car. All these random generation of keys is based on a seed value (often known as private key) which is unique and embedded into key fob.
Step 2. Brute force
The very next step after knowing about frequency bands is to start the attack with a good old Brute-force method. To get started, you of course need a laptop with the right algorithms programmed (the secret sauce). This when connected to the Software-radio hardware along with antenna and cheap antenna amplifier, is ready to hack any wireless system.
Brute-force attack involves cycling millions of code guesses at a rate of two to three a second until he found the one which successfully unlocked the car. Usually, it only takes less than 2 hours, but it varies from car to car.
Step 3. Optimize the bruteforce attacks (optional)
One doesn’t always have all the available time, and Brute force attacks can be filtered from millions to thousands, accelerating the whole process. However, this optimization requires pre-access to key fob.
Cesare created a hardware automation device to emulate large number of button presses at several key-presses per second and listened to the radio codes it transmitted. The solenoid based robot helped him assemble enough data to find patterns in the seemingly-random numbers, cutting the number of possible unlock codes from around 43 million to around 12,500.
Step 4. Discovering Backdoors
Like described earlier, the frequency codes are unique each time. But there are exceptions to this. There are service codes, intentionally designed by the manufacturer, to help unlock car in case they lost access to original key, or for other maintenance/emergency cases. This is essentially a backdoor a hacker can exploit. During brute-force, there are chances that you find such frequency codes which can be used repeatedly, without trouble. These codes provide a permanent backdoor to the hacker.
With hacker’s testing, the backdoor code worked as much as dozen times before it seized to work. There’s one more pre-requisite to making backdoor codes to work — The attacker must first identify a portion of the unlocking code that’s different for every vehicle. That means the hacker would need to eavesdrop on one lock or unlock command sent from the victim’s key fob, which is already described in step 3.
What it means for You and Your Car
Do you get to know if you got Hacked?
Of course, you probably lost your car or belongings. In case you’re lucky enough to not lose those, your key fob doesn’t work on the next use, and takes two or three button presses to again synch up with the car’s locking system.
What is the scale of the Car unlock Hack?
Imagine cars parked in a parking area where a hacker plans to run a full brute-force attack on the available wireless spectrum. With the calculated attack, hacker can create a unlock mania, unlocking several hours every few minutes. Imagine the possibilities and the scale. We’re not trying to scare you or anything but criminals could hire researchers to replicate the attack. And if that happens, the scale is too large to imagine.
The Hacker used sophisticate hardware which costed him over a grand but with newer hardware like HackRF, one can build similar hardware for under $200, making it more accessible to everyone.
Is your car vulnerable?
Honestly, no one, other than Cesare knows what makes and models are vulnerable. Even though researcher believes newer key fobs are way less vulnerable coz they use better algorithms. But there’s no guarantee you’re safe. Someone somewhere could develop algorithm to break it, some day.
Hacker has already reported the incident to CERT (Computer Emergency Response Team), which is working to alert the manufacturers of potential victims.
This is not the first time wireless unlocking systems have been hacked. They have become better with time and with HackRF, its only about to get worse.
Subscribe to us @geeknizer, Facebook Fanpage, Google+.
loading...
loading...